
A Deadly Midnight Alert: When Expensive Defenses Prove Ineffective in Practice
At midnight on a weekend at a mid-sized electronics manufacturer, the IT manager’s phone suddenly lit up with continuous alerts—multiple core servers had been encrypted by ransomware. The manager had been confident, since the company had recently invested in enterprise-grade firewalls and standalone backup storage systems. However, upon returning to the office, the manager found that these expensive devices were nothing more than disconnected IT silos when faced with a real attack.
The firewall did block the initial external attack. However, when attackers used an infected internal device to perform lateral movement, it had no control over the internal network and was rendered ineffective. Even more devastatingly, because the backup server remained constantly connected to the internal network, it was encrypted simultaneously as the production environment fell. This is the most common tragedy of traditional multi-vendor “patchwork” architectures: each piece of hardware is powerful on its own, but when disaster strikes, no one can coordinate the system as a whole.
The Broken Window Effect in the AI Era: Why Firewalls Are No Longer a Cure-All?
With the widespread adoption of generative AI, attackers can now launch cyberattacks at near-zero cost. Highly customized AI-generated phishing emails and rapidly mutating malware designed to evade signature-based detection have significantly increased the likelihood of traditional firewall-based “perimeter defense” being breached. Once a single employee device is compromised, ransomware can move freely across the network, spreading laterally as if the internal environment were unguarded. According to 2024 cybersecurity trend analysis, the average breakout time for attackers to initiate lateral movement after a successful breach has shortened to just 48 minutes, with the fastest cases taking only 27 minutes. In this new normal, where defenses can be breached at any time and attackers move faster than the limits of human response capability, assuming that internal networks are not secure by default, deploying Network Detection and Response (NDR), and ensuring air-gapped backups have become the only viable survival strategy for enterprises.
The Hidden Risks of a Patchwork Architecture: A Cross-Vendor Finger-Pointing Maintenance Nightmare
Traditional IT procurement practices typically source storage (NAS/SAN), networking (switches/routers), and cybersecurity defenses (firewalls/NDR) from different vendors, resulting in a patchwork architecture. Competitors and traditional vendors often won’t tell you that the hardware you purchase is only the foundation. The real challenge and the real cost lie in making these multi-vendor systems work together seamlessly to deliver coordinated defense. This is also why Gartner’s 2024 research indicates that up to 75% of enterprises are actively pursuing “vendor consolidation” to reduce operational complexity and improve cybersecurity effectiveness.
The limitations of this IT architecture are exponentially amplified in ransomware attacks. When abnormal traffic traverses switches, standalone storage systems cannot detect it in real time, and when the storage layer eventually detects abnormal data encryption, it cannot actively instruct switches to immediately disable specific ports. Not only that, but the golden window for incident response is often wasted on cross-vendor finger-pointing, which not only drains IT teams but also leads to escalating enterprise losses.
Unified Storage & Networking: A Self-Monitoring and Self-Defending Ecosystem
To resolve this deadlock, we must move beyond a “standalone, siloed mindset” and adopt a “Unified Storage & Networking” approach at the architectural level. Instead of purchasing fragmented hardware individually, enterprises should adopt an integrated ecosystem with deep interoperability and coordinated capabilities.
In this unified architecture, storage systems and network switches no longer operate in isolation. NAS acts as a “brain” with analytical capabilities, capable of proactively detecting abnormal network traffic or changes and anomalies in underlying write-layer behavior (e.g., snapshot entropy shifts). Meanwhile, the switch acts as the “hands and feet,” always and immediately executing commands and translating the brain’s instructions into physical-layer protection actions. This 1+1>2 system synergy transforms passive post-incident debugging into proactive self-alerting and response.
QNAP Integrated Storage & Networking Defense: From Proactive Threat Detection to Physical Isolation
To address the critical cybersecurity pain points of small and medium-sized businesses, QNAP offers an industry-rare, one-stop ecosystem integrating NAS and network switches (QSW series). Through native integration, it significantly lowers the barrier to deploy top-tier protection. More importantly, enterprises do not need to completely overhaul their existing core network architecture. By seamlessly replacing or adding QNAP devices and compatible switches in parallel at key nodes (such as server racks or backup silos), thereby enabling strong collaborative defense capabilities:
-
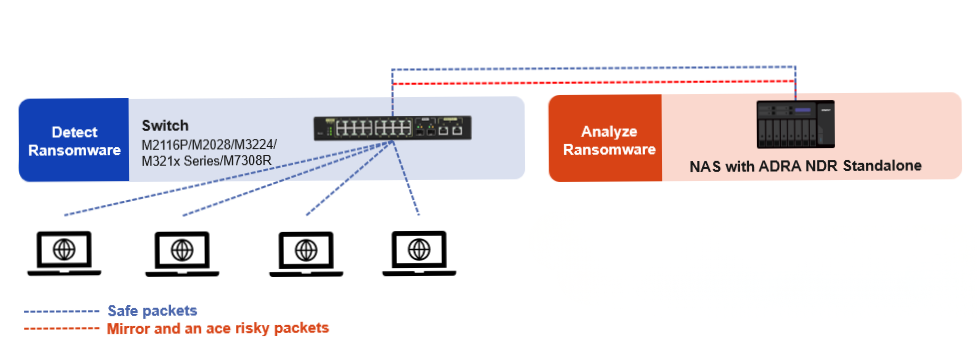
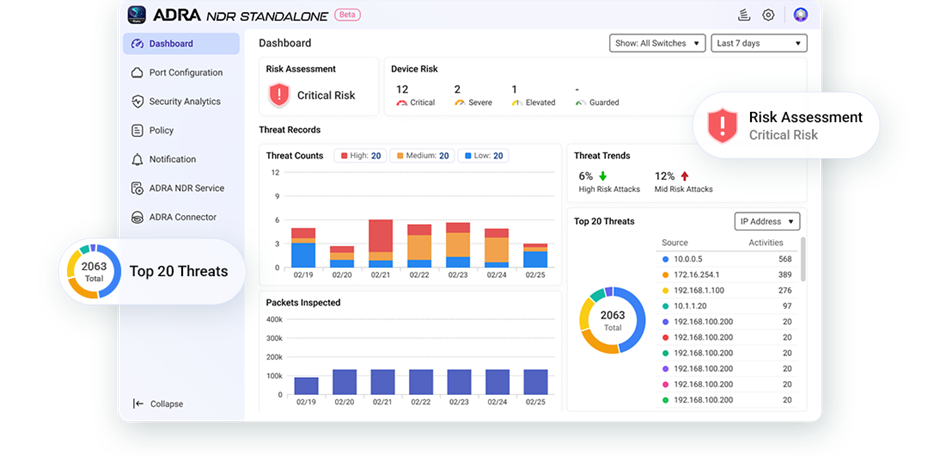
- ADRA NDR Standalone Active Coordinated Defense and Sub-second Blocking: Enterprises no longer need to invest in expensive, dedicated cybersecurity hardware. By simply installing the ADRA NDR Standalone Network Detection and Response app on a QNAP NAS, the ADRA NDR software can perform traffic analysis and threat assessment, while supported QNAP switches return to focus on packet forwarding and port-level blocking. Once ransomware activity is detected, whether in a dormant state or during lateral movement, the NAS instantly triggers the switch to isolate the affected device’s network port, enabling automated collaborative defense with a “detect-and-block” response.
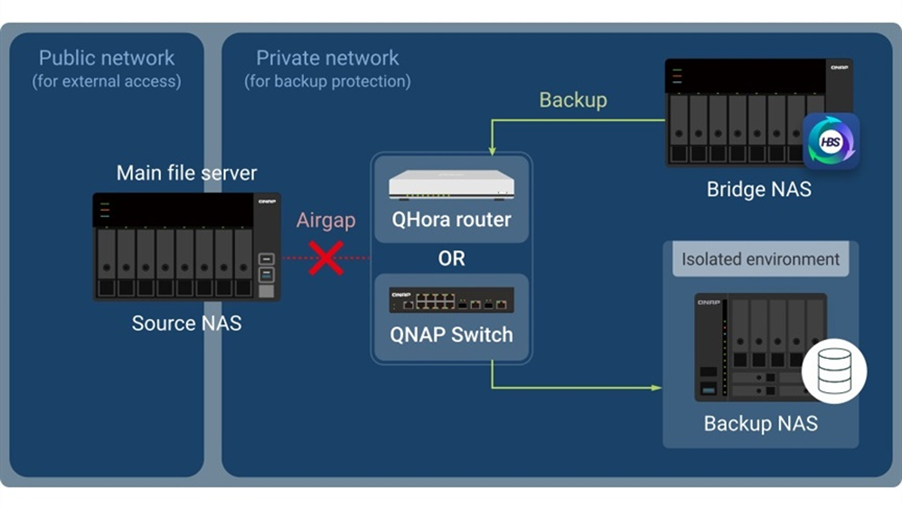
- True Physical Isolation (Airgap+) Backup: Even against the face of the most destructive attacks, the final line of defense remains impenetrable. By synchronizing QNAP’s HBS 3 backup software with the switch, the network port is only enabled when a backup task is initiated. Once the backup is completed, the switch automatically triggers a “Port Down” state to physically disconnect the backup device. Even if attackers obtain the highest-level privileges, they are unable to compromise a device that is physically disconnected from the network. This provides a higher level of protection than purely software-based snapshot protection.
| Switch Model | ADRA NDR Standalone Support | Airgap+ Support | Dual Support (Overlap) |
| QSW-M7308R-4X | ✅ | ✅ | ⭐ |
| QSW-M3224-24T | ✅ | ✅ | ⭐ |
| QSW-M3212R-8S4T | ✅ | ✅ | ⭐ |
| QSW-M3216R-8S8T | ✅ | ✅ | ⭐ |
| QSW-IM3216-8S8T | ✅ | ✅ | ⭐ |
| QSW-M2116P-2T2S | ✅ | ❌ | ❌ |
| Supported QNAP NAS Models & System Requirements | Learn more | Learn more |
Lower TCO: Transforming Hidden Debugging Costs into Competitive Advantage
Based on industry estimates, if an enterprise is breached and attackers perform lateral movement within the internal network, a traditional heterogeneous architecture may require 4 to 8 hours of manual investigation and debugging, or even several days waiting for responses from multiple vendors. By contrast, under QNAP’s “Unified Storage & Networking” architecture, the entire process—from anomaly detection and physical port isolation to backup and snapshot restoration—is fully automated. This not only minimizes RTO, but also ensures that enterprises maintain agile and reliable Disaster Recovery capabilities in the face of catastrophic impact.
Single Vendor Accountability refers to a model that provides a single management interface and a unified support channel. Enterprises can not only save on the high licensing costs of dedicated security appliances, but also eliminate cross-device integration and hidden debugging costs, which can reach up to 50% of the total costs in traditional architectures. IT teams can evolve from overwhelmed “firefighters” into decisive “strategic commanders.”
Conclusion: Building an Impenetrable Single-Vendor Ecosystem
“Are you investing in a collection of expensive IT silos, or building a unified storage and networking ecosystem capable of proactive alerting and active defense?” In the era of digital transformation, cyberattack techniques are evolving rapidly. If your defense mechanisms remain stuck in siloed hardware-based defenses, failure is only a matter of time. Choosing QNAP’s one-stop storage & networking architecture is more than just an equipment purchase—it is an investment in a stable, reliable, and self-healing foundation of enterprise resilience.