
In April 2026, an urgent cybersecurity advisory issued by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) sent shockwaves through the global manufacturing industry. The advisory revealed that a hacker group linked to the Iranian government has been actively exploiting a Programmable Logic Controller (PLC) vulnerability—CVE-2021-22681, first disclosed in 2021—to carry out ongoing attacks against industrial control systems and critical infrastructure in the United States, Israel, and other regions.
This vulnerability affects Rockwell Automation’s Logix series PLCs and allows unauthenticated remote attackers to download and modify PLC control logic without authorization. It carries a severity rating as high as 10.0. In other words, an attacker can remotely and stealthily take control of industrial systems from another country and issue the command: “Shut down operations.”
What’s striking about this attack is not the sophistication of the vulnerability itself, but its age—five years. In a typical IT environment, a known vulnerability from five years ago would have been patched long ago through routine updates. However, within Operational Technology (OT) environments, this same vulnerability can still be exploited at scale even five years after its disclosure.
Why Is It So Hard to Patch Legacy Factory Equipment?
To understand this issue, it’s essential to first understand the inherent nature of OT environments and the lifecycle of their products. Industrial equipment in the field differs significantly from office computers. Devices such as PLCs, Supervisory Control and Data Acquisition (SCADA) systems, and industrial robots often run on legacy operating systems dating back 10 to 20 years. Furthermore, vendors do not recommend arbitrary firmware updates, as any unforeseen change could bring an entire production line to a halt. At the same time, small and medium-sized manufacturers often lack dedicated cybersecurity personnel, and their production environments are frequently not properly segmented, making it difficult to contain incidents within isolated network segments.
This is the core paradox of OT Cybersecurity:
| The Reality of OT Environments | Assumptions in Traditional IT Cybersecurity |
| Equipment cannot be easily rebooted | Regular patching is a baseline assumption |
| Connectivity is for production monitoring, not cybersecurity | Network segmentation is standard practice |
| Downtime is measured in minutes, with costs easily reaching millions | Short service interruptions are acceptable |
| Equipment lifespans reach 10–20 years | Systems are replaced every 3–5 years |
When Rockwell first recommended a mitigation for CVE-2021-22681, the proposed fix was a firmware upgrade. However, for most affected factories still in operation, scheduling an unplanned firmware update is effectively equivalent to deliberately forcing a production shutdown. The cost of such downtime is often even harder to justify to management than the risk of continuing operations under potential cyber exposure. The result: even five years after the vulnerability was disclosed, a large number of PLCs remain exposed to threats.
The Solution Isn’t a Patch, but “Virtual Patching”: Turning the Network into a Security Boundary
If devices cannot be patched directly, what are the options?
The cybersecurity industry offers a well-established approach for this challenge, known as Virtual Patching. The core concept is: instead of applying patches directly to the device, you build a “network-level defense layer” around it—so that malicious traffic targeting known vulnerabilities is identified and blocked before it ever reaches the target device.
The workflow of virtual patching is as follows:
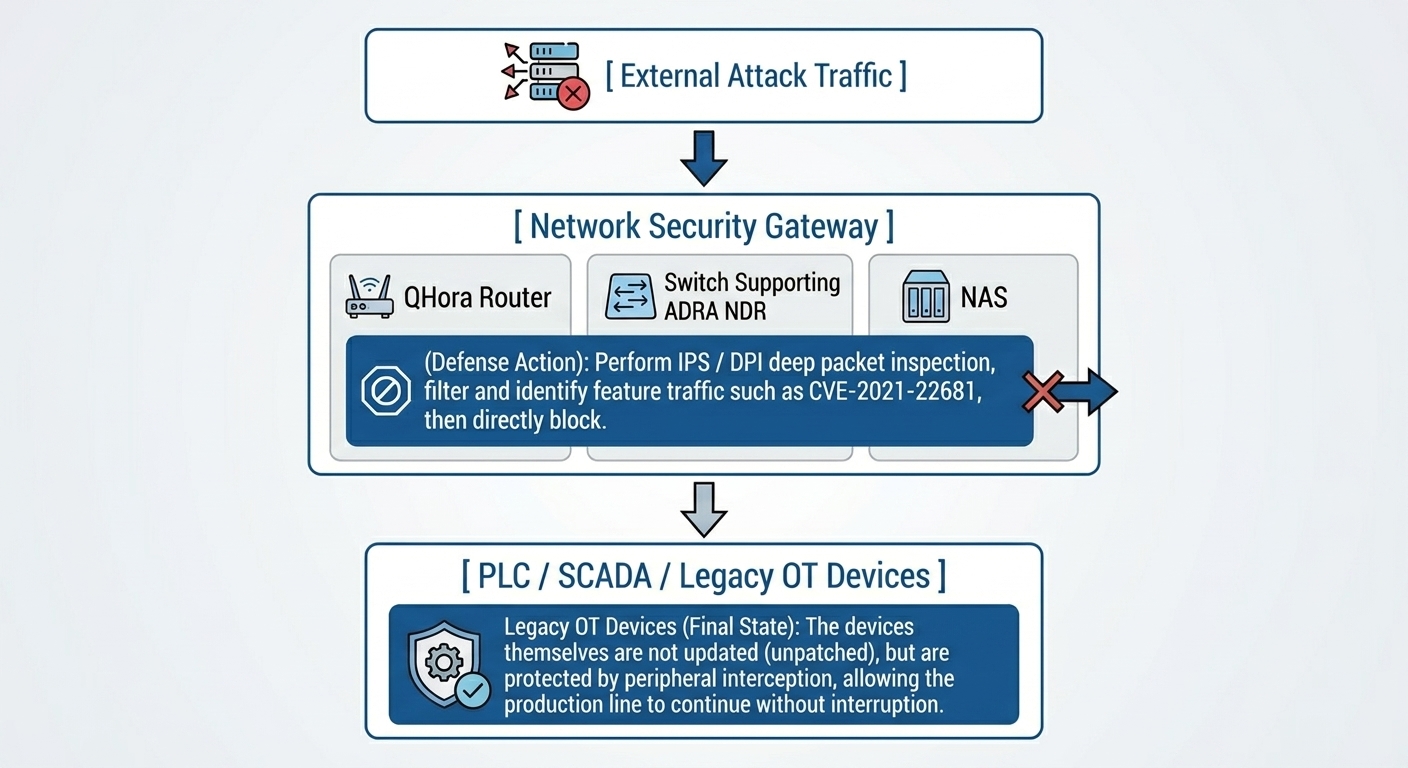
By integrating Zero Trust Microsegmentation, OT environments can be further partitioned into multiple isolated security zones. Even if an attacker compromises one node, they are unable to move laterally across the entire factory network. This is the practical execution of what the industry defines as “Defense in Depth”.
QNAP Helps Build a Multi-Layered Defense-in-Depth Framework for OT Environments
QNAP’s IT/OT cybersecurity solutions are built around the above principles, delivering a defense architecture that can be implemented in a phased rollout and that aligns with international industrial cybersecurity standards such as NIST CSF 2.0 and IEC 62443.
1. ADRA NDR Standalone: Turning NAS into Your OT Detection Hub
QNAP ADRA NDR Standalone is a cybersecurity solution that decouples Network Detection and Response (NDR) capabilities from switches and deploys them onto a NAS platform. By integrating NAS with compatible switches, it delivers enhanced visibility into OT network traffic. Its core capabilities include:
- High-Performance Packet “Pre-Filtering” Detection Mechanism: Unlike traditional cybersecurity appliances that may degrade network performance, ADRA NDR performs deep inspection only on packets exhibiting anomalous characteristics. This approach preserves high throughput and low latency in OT networks while enabling effective detection of “lateral movement” by malware.
- Multi-Layered Threat Trapping Mechanism: Virtual honeypots simulating common services such as SSH, SMB, and HTTP are deployed within the internal network. Once a latent attacker or malware attempts to probe these decoy nodes, the system immediately triggers an alert and tracks the attack source.
- Automated Containment & Response: When a device is identified as high-risk or compromised, ADRA NDR can integrate with QNAP managed switches to automatically isolate the affected node in real time. This ensures that a single compromised node does not spread across the entire production line—achieving the goal of “precise threat containment without disrupting operations.”
The biggest advantage of this solution is that enterprises do not need to invest in expensive dedicated NDR hardware and licensing. By simply installing the free ADRA NDR application on a QNAP NAS and pairing it with compatible switches, organizations can quickly build an enterprise-grade internal network defense system—without impacting OT operations.
2. QHora Routers: The Core Enforcement Point for Micro-segmentation
QNAP QHora routers support L3–L7 firewall protection and feature Intrusion Prevention System (IPS) and Deep Packet Inspection (DPI), enabling them to:
- Identify and block CVE-related traffic patterns to enable network-layer protection through virtual patching.
- Enforce OT/IT network segmentation using VLANs and ACLs to prevent cross-segment lateral movement.
- Support Qbelt VPN (DTLS encryption) to ensure secure access to factory equipment for remote maintenance personnel.
3. NAS: The Last Line of Defense for IT/OT Convergence
To address the issue of system recovery after a compromise, QNAP NAS provides:
- Airgap+ Isolated Backup: Keeps backup environments from continuous network exposure, preventing ransomware from subsequently encrypting backup data and ensuring a secure isolated data environment.
- WORM (Write Once, Read Many) Immutable Storage: Ensures that critical OT data such as production records and equipment logs cannot be tampered with or deleted.
- Snapshot Technology: Enables rapid restoration of systems to a pre-attack state after an incident, significantly reducing Recovery Time Objective (RTO).
4. Additional Defensive Measures and Recommended Actions
- Disconnect from External Networks (Most Important): Check whether the PLC has a public IP address or has been exposed to the external network. Unless absolutely necessary, PLCs must not be directly connected to the internet.
- Use VPN and Multi-Factor Authentication (MFA): For remote maintenance, encrypted VPN connections must be enforced together with MFA. Direct exposure of specific TCP ports (e.g., 44818) to the internet must be strictly prohibited.
- Micro-Segmentation: Implement firewalls to strictly isolate the factory control network (OT) from the corporate office network (IT).
- Regular Offsite Backups: Ensure up-to-date backups of PLC logic programs are available so they can be quickly restored in the event of deletion or tampering.
Conclusion: From “Asset Management” to “Risk Mitigation” — Winning Through Cyber Resilience
In 2026, the success of Digital Transformation (DX) in manufacturing is no longer determined solely by production efficiency, but increasingly by “Cyber Resilience”. The greatest danger does not lie in new hacking techniques, but in our tendency to overlook long-standing security debt—issues that already have solutions, yet remain unaddressed due to inconvenience.
QNAP does not offer an out-of-reach hardware stack, but rather a low-intrusion, high-visibility, and phased-rollout pathway to IT/OT integrated defense. It starts with uncovering hidden assets, moves on to establishing virtual patching defenses, and culminates in an automated response framework. Each step transforms your production line from a reactive, attack-prone state into a proactive defense posture.
Start now by reviewing your initial security debt—and start paying down accumulated risk in your smart factory.
Download Now: [QNAP IT/OT Cybersecurity Solutions White Paper]